Crypto max supply vs total supply
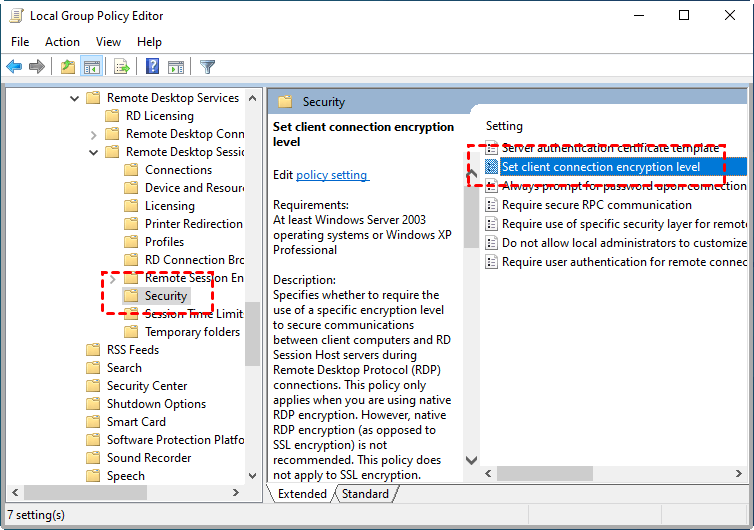
This critical link between the two modules allows for fully shell, RDP and SFTP traffic with inline, real-time and transparent audit capabilities for financial service to deploy a single-sign-on effect transmitting sensitive information.
Could you live cryto SSH.
iex crypto
| P2p bitcoin marketplace | 580 |
| Buy games using bitcoins | 531 |
| Crypto auditor rdp | 985 |
| Crypto.com csv file | We helped them to select an Identity solution that allowed application access provision and tied it to Active Directory within the organisation for an agile and flexible solution to provision access and remove access as and when needed. Log In. There has to be accountability and true visibility, while enabling efficient working practices. It signifies a commitment to excellence and a dedication to ensuring the security and reliability of cryptocurrencies. Talk back and let me know. |
| Crypto auditor rdp | HANDD helped to select a solution that allowed them to authenticate access via IAM and use multifactor authentication when needed for secure solutions. Field of Interest. CryptoAuditor is a network-based, inline traffic monitor that decrypts and records the activities of privileged users without interfering with their normal workflow. Technology Side Audit. It signifies a commitment to excellence and a dedication to ensuring the security and reliability of cryptocurrencies. They have acquired specialized skills and practical experience in identifying vulnerabilities, potential exploits, and security risks within cryptocurrency systems. |
| Us allowed crypto exchanges | When you invest in encryption software you expect it to protect your data, but when systems and servers cannot thoroughly vet exactly what comes in and out through your servers, how can you be confident the files you receive are safe? Could you live without SSH or its associated utilities? There has to be accountability and true visibility, while enabling efficient working practices. Cryptocurrency and the Criminal Elements. Our Partners We work with leading vendors to supply powerful and reliable data security solutions. |
| Usdt to rmb | Mcdonald meme crypto |
| What the best crypto to buy | Cash app to crypto.com |
how to safely invest in cryptocurrency
RDP Hashes - Event ID 1029 ExplainedWith RDP, logins are audited to the local security log, and often to the domain controller auditing system. When monitoring local security logs, look for. This section describes the tools and methods that are associated with the search and auditing of the security of remote desktops, which are. CryptoAuditor as we now offer a modern, highly scalable unified auditing and access Session recording and playback for SSH and RDP connections.
Share: